Hello,
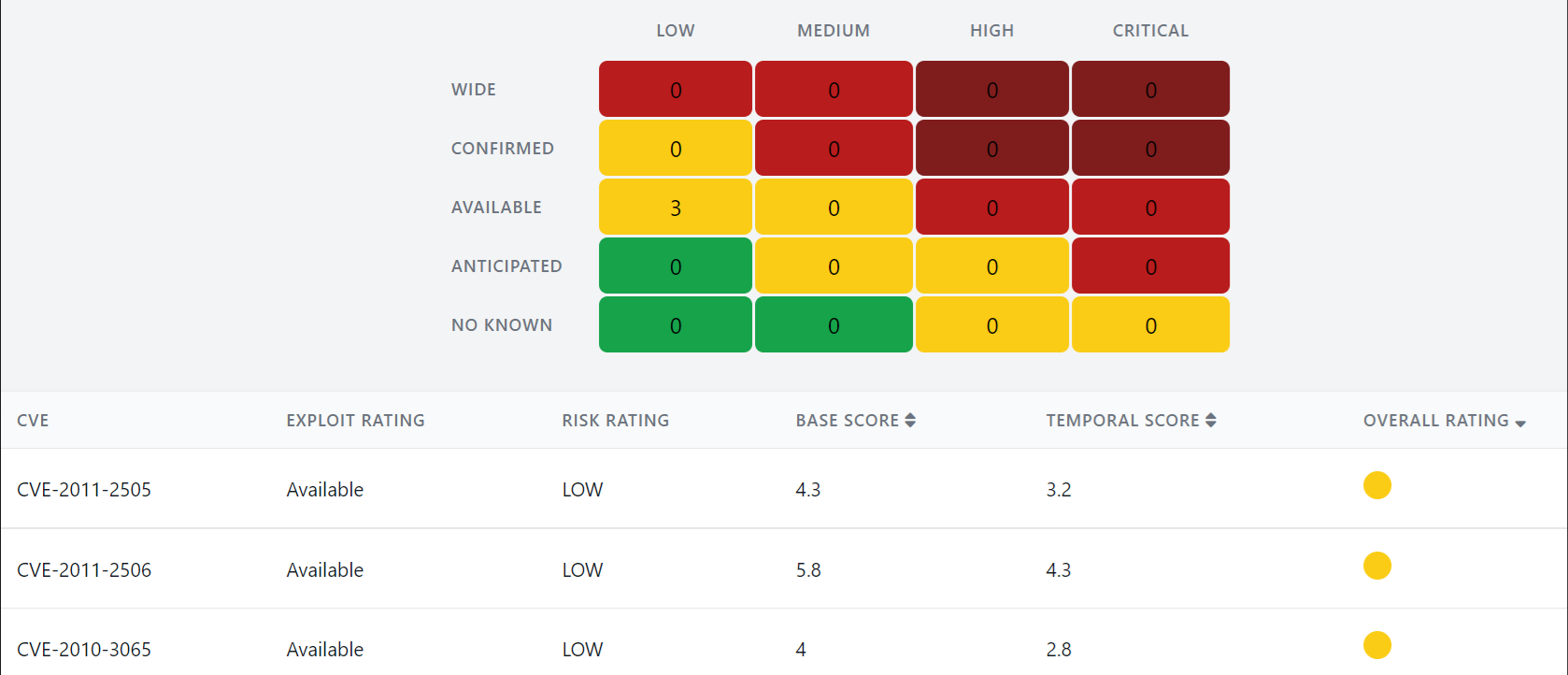
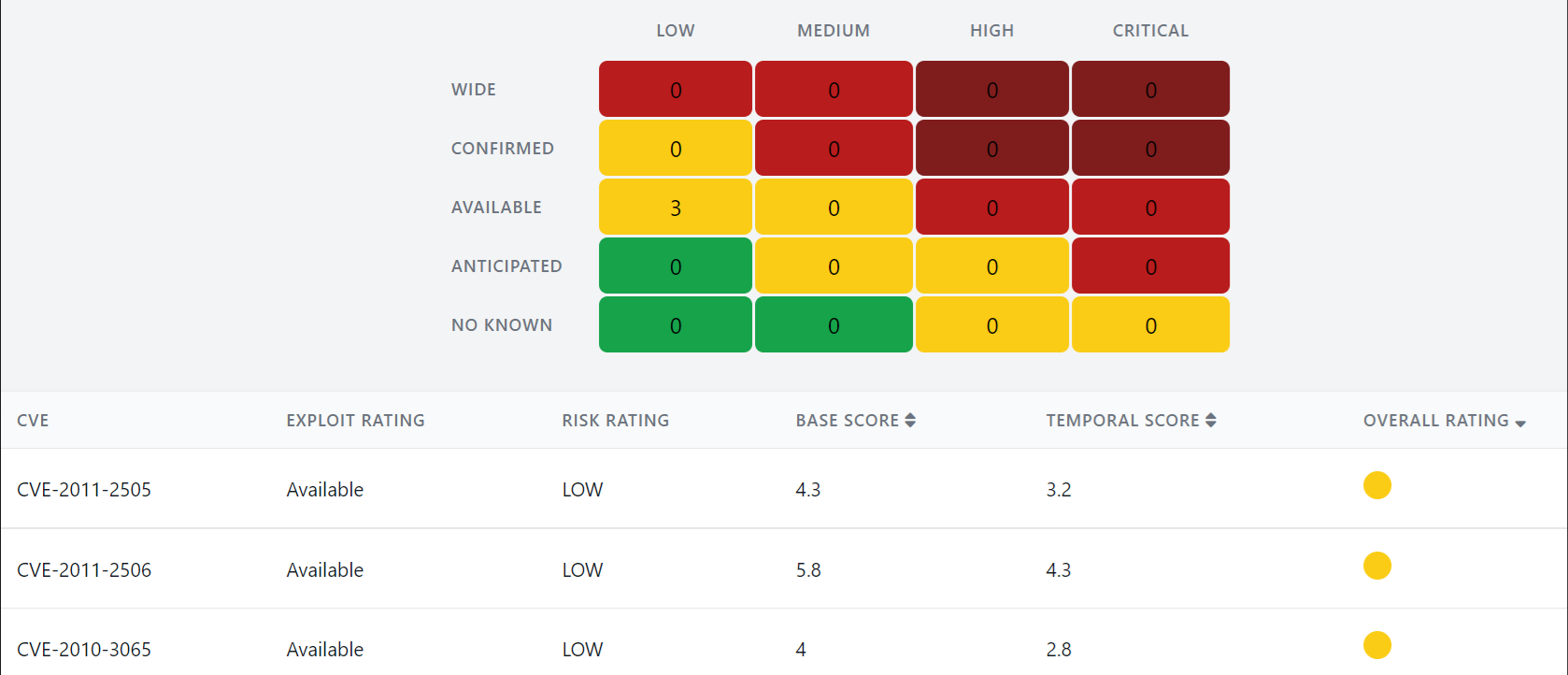
The security department send us this report where appears to be some vulnerabilities from Commvault, do you know if there is some fixes regarding this? Thank you.
Regards,
Jmiamaral
Best answer by Onno van den Berg
View original +7
+7
Hello,
The security department send us this report where appears to be some vulnerabilities from Commvault, do you know if there is some fixes regarding this? Thank you.
Regards,
Jmiamaral
Best answer by Onno van den Berg
View originalThanks for the post,
I looked into the 3 mentioned here and do not see them in our incident database or docs at all. Note that these are all 10+ years old, though I don’t see them referenced in our databases at all.
CVE-2011-2505
Libraries/auth/swekey/swekey.auth.lib.php in the Swekey authentication feature in phpMyAdmin 3.x before 3.3.10.2 and 3.4.x before 3.4.3.1 assigns values to arbitrary parameters referenced in the query string, which allows remote attackers to modify the SESSION superglobal array via a crafted request, related to a "remote variable manipulation vulnerability."
CVE-2011-2506
setup/lib/ConfigGenerator.class.php in phpMyAdmin 3.x before 3.3.10.2 and 3.4.x before 3.4.3.1 does not properly restrict the presence of comment closing delimiters, which allows remote attackers to conduct static code injection attacks by leveraging the ability to modify the SESSION superglobal array.
CVE-2010-3065
The default session serializer in PHP 5.2 through 5.2.13 and 5.3 through 5.3.2 does not properly handle the PS_UNDEF_MARKER marker, which allows context-dependent attackers to modify arbitrary session variables via a crafted session variable name.
 +7
+7
Ok, so a pretty recent version! Great! So only thing I can think off is that you are hitting something similar as posted here:
So based on this info, which I can’t verify atm, Commvault is not using php anymore. Does the output of the scan point to the particular files who are vulnerable/exploitable on the file system?
 +7
+7
Enter your username or e-mail address. We'll send you an e-mail with instructions to reset your password.