Hi,
I saw Commvault bring Commserve Linux feature in Feature Release 25. So i wanted to test it. I created Linux package as described here;
I installed fresh RHEL 8.3. I’m trying to setup as described here;
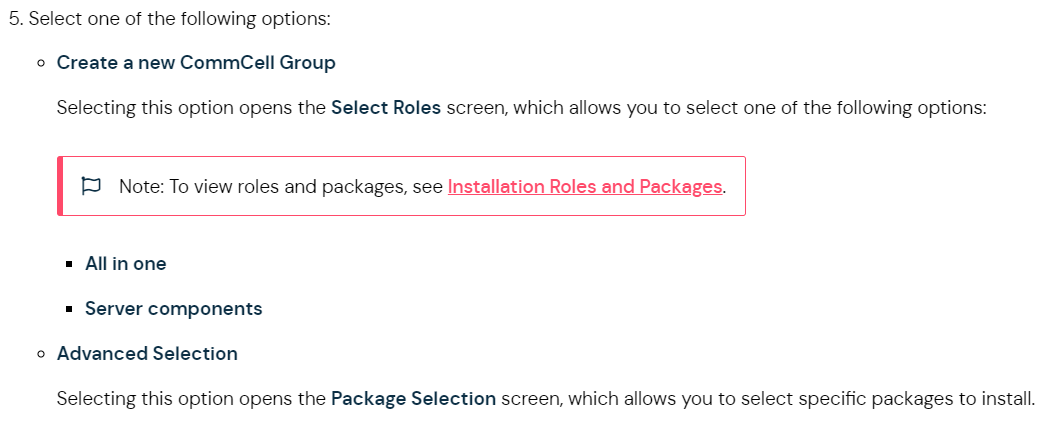
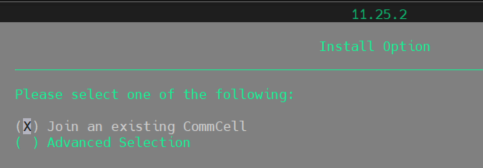
In my screen i don’t see Create a new CommCell Group option. My screen;
Could you help me for this issue. Thank you.
Best answer by Carl Manzi
View original