As maybe know the last day’s a lot of actions needs to performed regarding the Log4j vulnerbility. Is this also been used in the Commvault software?
If so is there a patch/fix upcoming?
Best answer by Stuart Painter
View originalAs maybe know the last day’s a lot of actions needs to performed regarding the Log4j vulnerbility. Is this also been used in the Commvault software?
If so is there a patch/fix upcoming?
Best answer by Stuart Painter
View originalThe developer of log4j said (on Friday) that 1.x is not vulnerable, via twitter.
Log4j 1.x does not offer a look up mechanism. Log4j 1.x sends an event encapsulating a string message to a JMS server. That is it. The attacker can supply whatever string he chooses but it remains a String. So not the same. At all.
Thanks Brock, although I’m not sure that list is complete. This server has multiple log4j JAR files and it doesn’t have those packages installed. Hopefully it’s not used in these, either.
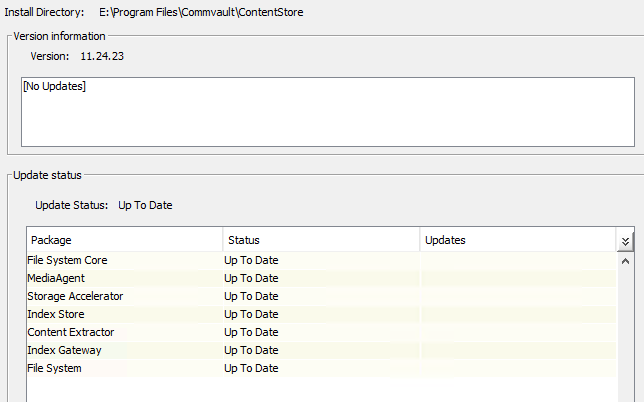
C:\>dir /s E:\*log4j*.jar
Volume in drive E is Server Applications
Directory of E:\Program Files\Commvault\ContentStore\CVAnalytics\DataCube\app\webapps\server\WEB-INF\lib
06/22/2021 05:12 AM 481,403 apache-log4j-extras.jar
06/22/2021 05:13 AM 525,106 log4j.jar
06/22/2021 05:14 AM 16,710 slf4j-log4j12.jar
3 File(s) 1,023,219 bytes
Directory of E:\Program Files\Commvault\ContentStore\CVCIEngine\CvPreviewHome\app\webapps\server\WEB-INF\lib
06/22/2021 05:12 AM 481,403 apache-log4j-extras.jar
06/22/2021 05:13 AM 525,106 log4j.jar
06/22/2021 05:14 AM 16,710 slf4j-log4j12.jar
3 File(s) 1,023,219 bytes
Directory of E:\Program Files\Commvault\ContentStore\CVCIEngine\CvPreviewHome\webapps\CvContentPreviewGenApp\WEB-INF\lib
11/03/2021 05:29 PM 525,110 log4j-1.2.17.jar
1 File(s) 525,110 bytes
Total Files Listed:
7 File(s) 2,571,548 bytesFor what it’s worth, a scan of a server with the Cloud Apps package installed didn’t find any results for *log4j*.jar.
Hi All
We have been running deeper reviews since this was reported, and we will be posting an official notice on this CVE within the next few hours to our BOL Security notices page.
As noted in some of the earlier threads, there is not an active, operational risk.
We do not actively use or load the Log4j service.
Several of the installed client packages will show up under a file scan with the affected files as part of the library - but those are static passive files as part of some of the libraries.
The affected clients
The notice will include new hotfixes that can be used to remediate those clients and we will automatically remove the affected files.
Thank you
Brock
(Brian Brockway, Global CTO, VP, Commvault)
There is a KB article posted in MA, but it says that v1 isn’t affected; it was last updated nearly two days ago, though.
Hello
Commvault must publish an official document for this issue.
If you run Greenbone against Commvault it finds heaps of older, unpatched open source software packages like the log4j 1.x. We need to hold them more accountable.
I believe the page above was modified to remove references to logj4 under the libraries used.
EDIT: Apologies, I was searching LOGJ4 instead of LOG4J, user error. ![]()
doing a file search in the commvault install folder I can see there’s multiple log4j libraries in the
ContentStore\MessageQueue\lib\optional folder, which included version 1.2.17.
According to this CVE log4j 1.2.0 to 1.2.17 are impacted by this via CVE-2019-17571
https://nvd.nist.gov/vuln/detail/CVE-2019-17571
Can you confirm if commvault is indeed not impacted by this or patch will be provided to mitigate this issue.
Add me to the list of people demanding a formal statement.
If log 4j 1.x is EOL , why did Commvault use it in its packages ?
Are we 100% sure that log 4j 1.x versions are not impacted by this vulnerability or we are saying it because it is EOL ?
Please share the official response from CommVault regarding this vulnerability ?
Regards, Mohit
Hi to all,
Is there any official note by Commvault?
regards
michele
good news that CV software isn’t affected because version log4j 1 is used.
But on the other hand:
I agree, I came here to find confirmation of this and was expecting an official statement that I can take to our security team. I really encourage Commvault to get that out by Monday, so that Internet searches will find it.
![]()
Hi
Yes, we’re certainly seeing lots of activity in Customer Support here over the last 24 hours or so with this one.
My understanding is that while we do have log4j packages present in Commvault, these are earlier versions and this current vulnerability CVE-2021-44228 only affecting certain v2 versions.
Thanks,
Stuart
Thanks
Hi
Thank you for the question, there is a lot of activity around this one right now.
Commvault is not affected by this log4j vulnerability, tracked as CVE-2021-44228.
After inspection we found that the Commvault platform is not using the log4j packages versions as documented in the vulnerability and is therefore not affected by this vulnerability.
Thanks,
Stuart
Enter your username or e-mail address. We'll send you an e-mail with instructions to reset your password.