Hello,
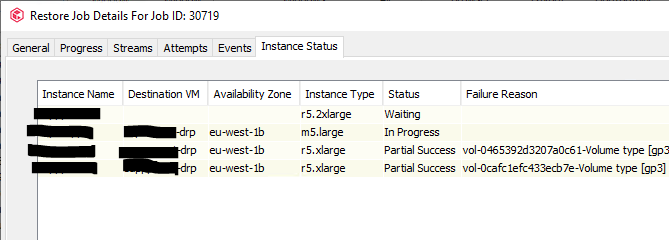
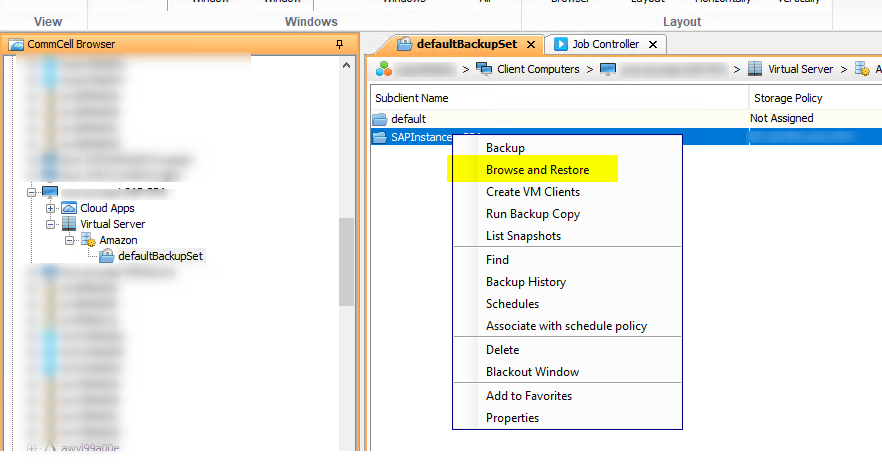
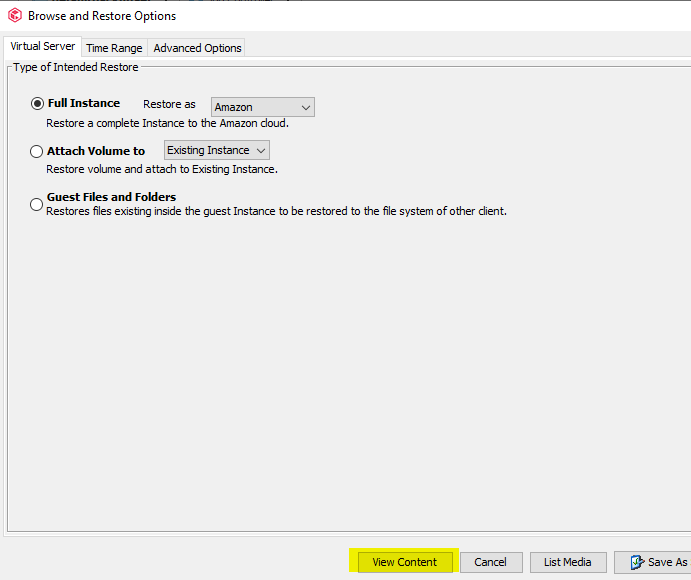
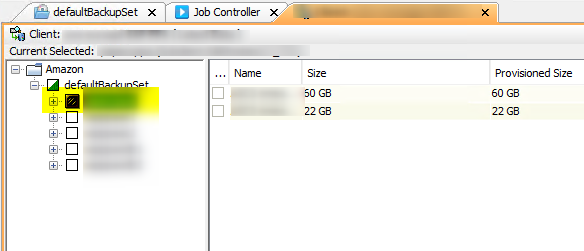
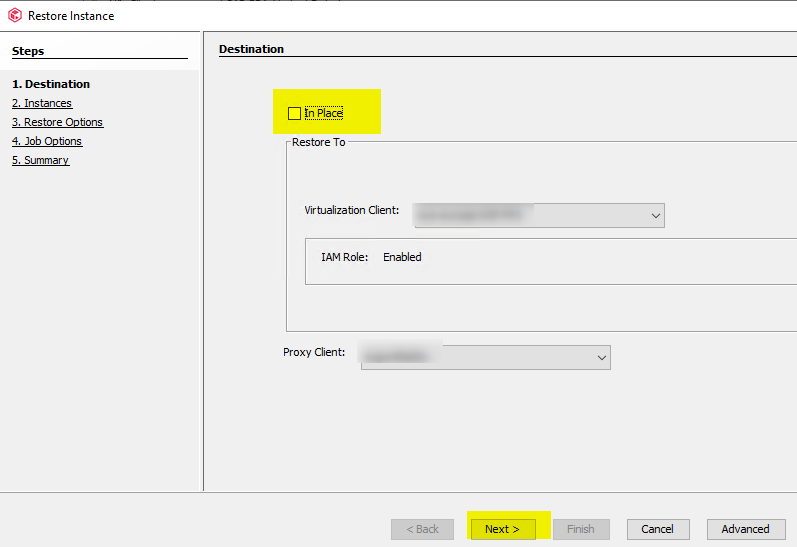
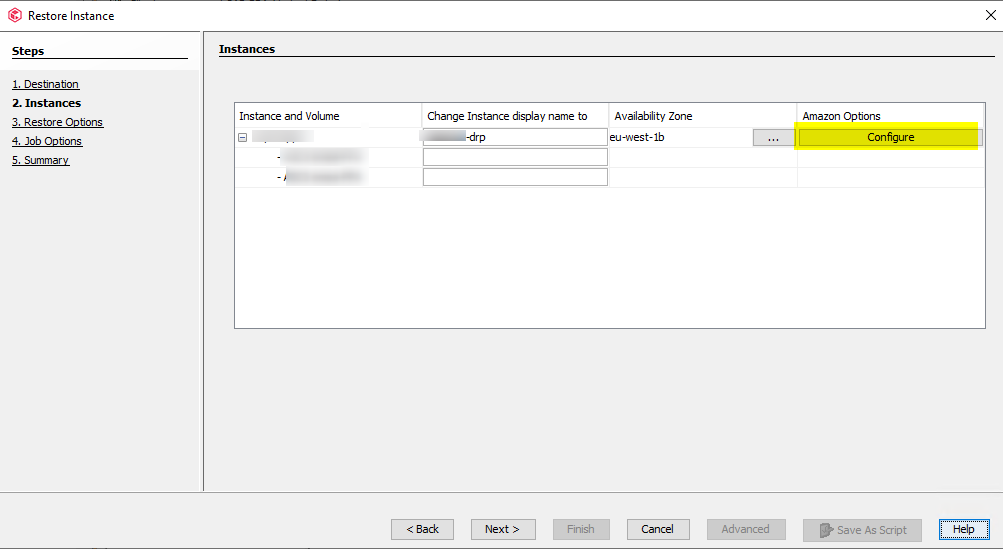
I try to restore an AWS instance using the out of place option.
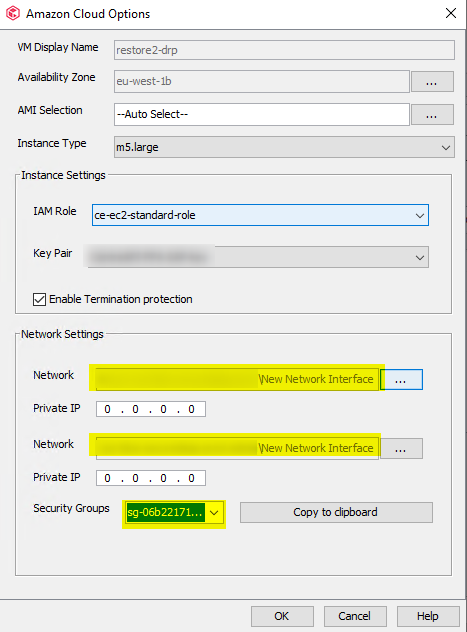
I have modified only the name of the instance and leave all default settings.
I am restoring on the same Availability zone.
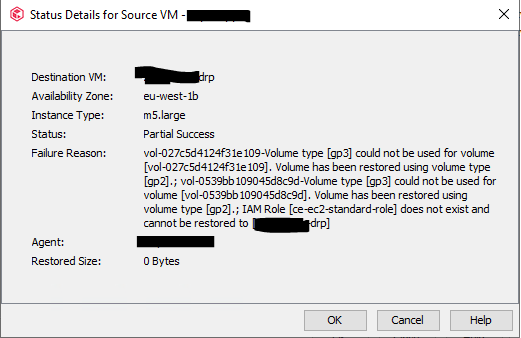
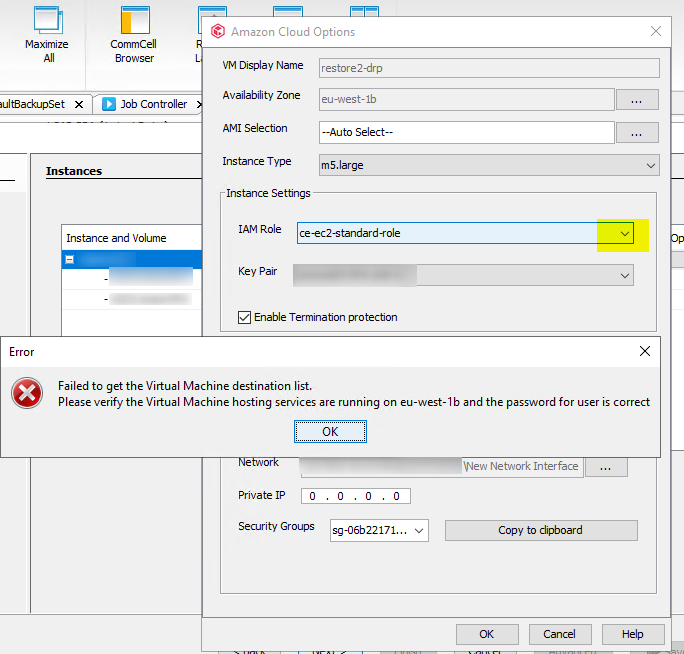
I have this error message
does anyone have some experience on AWS restorations ?
vol-064d51e6343cc439b-Volume type [gp3] could not be used for volume [vol-064d51e6343cc439b]. Volume has been restored using volume type [gp2].; vol-061d8c0b7a9efc2da-Volume type [gp3] could not be used for volume [vol-061d8c0b7a9efc2da]. Volume has been restored using volume type [gp2].; IAM Role [ce-ec2-standard-role] does not exist and cannot be restored to [myinstance-restore]
thank you !