Hi all,
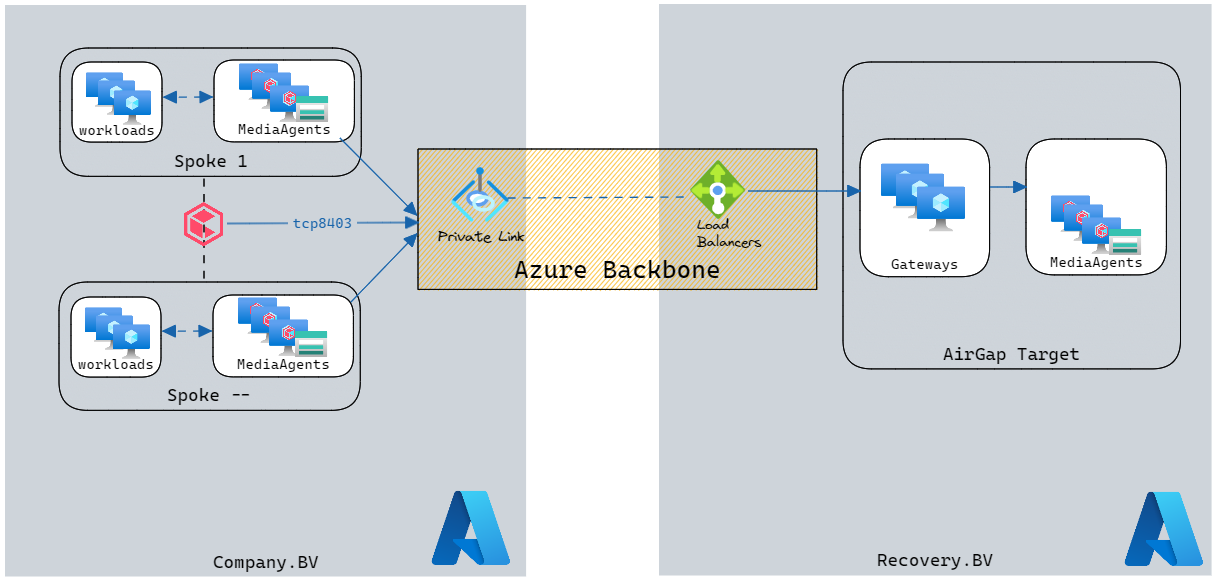
We are creating an AirGap Solution towards another Azure tenant.
The AirGap solution contains multiple Network Gateways and MediaAgents with Storage Accounts attached.
Question:
1. Does anyone have experience using a Azure Private Link Service to sent AirGap Copies using the Azure Backbone Network?
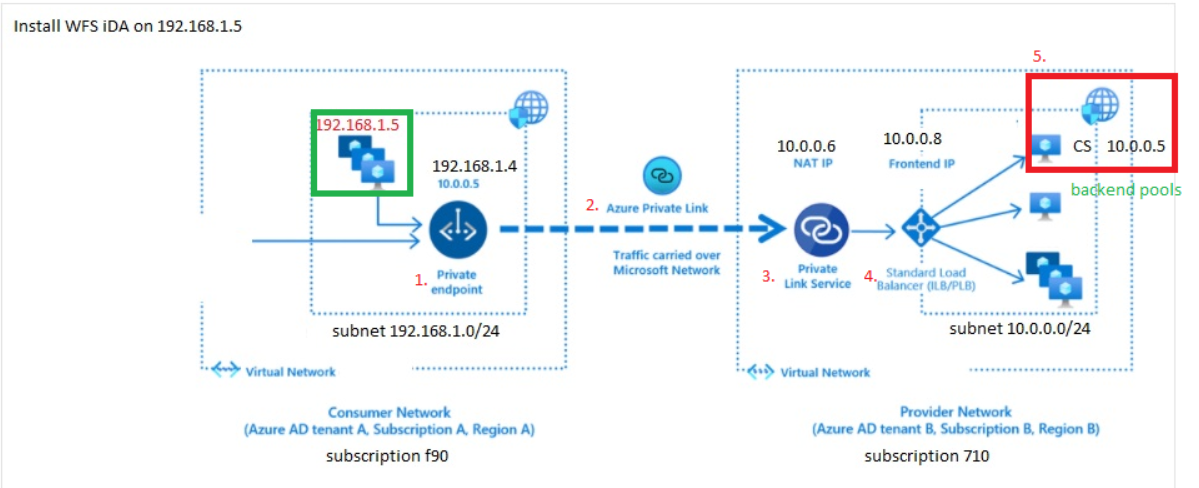
2. If yes, how did you configure the Azure Load Balancing?
How I think it’s working: