Hello All,
I am trying to setup an integration between Azurestack and Commvault but even after following the URLs below and Azure powershell was installed it keeps on giving the error as below :
Add hypervisor failed. Validate VS credentials failed. Error [100:Failed to connect to virtual machine host [https://portal.azslab.local/a84fbca7-3bba-4c58-8d6a-1426278db8a2/?microsoft_azure_billing_provider=58640284-879b-4ce9-b81f-42f5e38d14b6?SubscriptionId=56BD8014-E521-4DD8-B4CD-A29C05712C2B] as user [Azurestack-commvaultbackup-1272060f-2ae5-40ab-87d4-cc0cf9df3e93] from access node [pcommsrvazs01]. [Failed to get AzureStack URLs, Please make sure Azure PowerShell is installed on the proxy]]
I have an ADFS server for authentication with Azurestack. Please guide me on the error.
Environment:
An all in one physical server has been deployed as commserve acting as VSA Proxy for azurestack :
Powershell installed :
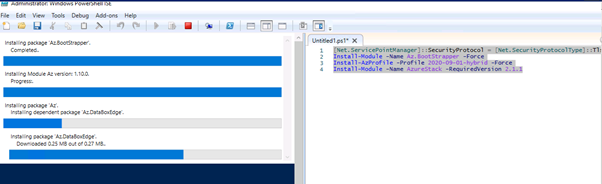
Run Powershell in an elevated prompt
Powershell Gallery access (can be done with Internet Access & Offline too)
Install-module -Name PowerShellGet -Force
Get-PSRepository -Name "PSGallery"
If the repository isn't registered, open an elevated PowerShell session and run the following command:
Register-PSRepository -Default
Set-PSRepository -Name "PSGallery" -InstallationPolicy Trusted
Procedure - AD FS
- Create a service principal for AD FS. Refer to: Create Service Principal for AD FS.
- Assign role to the newly created service principal. Refer to: Assign role to service principal.
- Log on to the Azure Stack Hub portal. Use the service principal with the following command:
Add-AzureRmAccount -EnvironmentName "<AzureStackEnvironmentName>" -ServicePrincipal -CertificateThumbprint $servicePrincipal.Thumbprint -ApplicationId $servicePrincipal.ApplicationId -TenantId $directoryTenantId
- Optional: You can use the predefined Contributor role or define a custom role to specify more limited permissions that can be used for backup and restore operations, either for a specific resource group or for the subscription as a whole. At a minimum, include the permissions listed in the CVBackupRole.json file.
Download the CVBackupRole.json file, which contains minimal permissions needed for Azure backup and restore operations.
Use a JSON editor to modify the following entry and change #SubscriptionID# to your subscription ID:
"AssignableScopes" : ["/subscriptions/#SubscriptionID#"]
To complete the setup of the Azure Stack Hub virtualization client in the CommCell Console, you will need the following:
- Application name
- Application ID
- Subscription ID
- Tenant ID (Directory ID)
- Application key.
- For Hypervisor name or Client name, type a descriptive name for the hypervisor.
- For Authentication Type, select the deployment type from the following:
- Azure Active Directory
- Active Directory Federation Services
- For Resource Manager URL, type the web site address that will be used to communicate with your Azure Stack Hub environment.
- Enter host or account information:
- Subscription ID: Enter the subscription ID for your Azure account.
- Tenant ID: Enter the tenant ID associated with the Azure account.
- Application ID: Enter the application ID associated with the tenant.
- Application password: Enter the password for the application.
- From the Access node list, select a previously deployed proxy
The VSA proxy must be an Azure virtual machine in the region to be protected.
- Click Save.