We are running a POC for seeding an AWS S3 bucket which will act as DASH target. For the seeding of data, we are using the AWS Snowball device. We have two goals in POC,
- Seed the OnPrem backup data to AWS S3 using Snowball device and ship it to AWS. Once seeded to S3 bucket, test restores from S3 and also validate the next DASH job to S3 only transfers unique data after deduping.
- Copy the DASH data from S3 to Snowball Device, ship the device to On-Prem. Perform restores from the Snowball device.
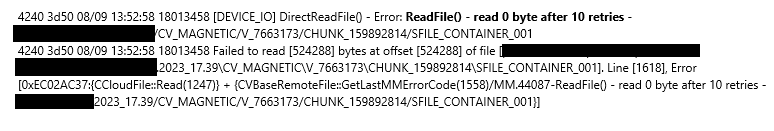
We have successfully completed the first part of the POC and need to initiate the second phase. But before shipping the snowball device to AWS, we ran a data verification job on the Snowball to confirm all the seeded DASH jobs are in readable state. The job failed since Commvault was unable to read any data from the Snowball device, and we were getting read errors. We opened case with CV Support, and after confirming there was no issue with Commvault, we engaged the AWS Support. They mentioned that the data on the snowball device is encrypted by default and Commvault is not decrypting the data before attempting to read.
Below are the logging errors found in ScalableDDBVerf.log.
Now my question is how we can ensure that Commvault can decrypt the data first on the snowball before it attempts to read the data for data verification or restore. We already enabled the Commvault encryption on the Global DDB policy and the device is also encrypting the data using its own default encryption which we cannot disable. Is there a way to provide the AWS decryption key to Commvault so it can read the data from the device. I found the below additional setting but was not sure if I could use this for a Snowball device.
Enabling Server-Side Encryption with Amazon S3-Managed Keys (SSe-S3) (commvault.com)
This is not only an issue with POC, but also in future if we ever want to restore a large or entire set of data from S3 DASH copy. We would like to use the snowball for restores instead of restoring over the WAN which has low restore speeds.