Hi All,
I have deployed Storage Accelerator on a Linux host but it does not seem to be working as the cloud team states that data transfer is still occurring cross-account.
My setup is as follow:
Client - Account 1
S3 Bucket Account 1
Media Agent (DDB) - Account 2
The Storage Pool is created with DDB enabled on the Media Agent in Account 2. The idea is to have the client writing to the S3 bucket in the same account.
The Media Agent can access the bucket across the account as backups are completing. I tested uploading a file from the client to the S3 bucket by using "aws cli s3 upload" command which completed successfully.
I also added the ARN credential on the cloud library for Storage Accelerator.
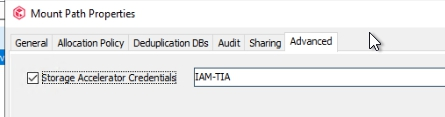
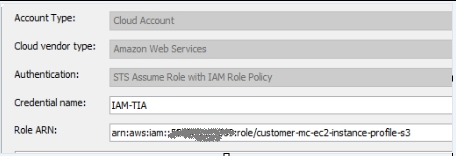
Is the format of this correct?
arn:aws:iam::123456789012:role/customer-mc-ec2-instance-profile-s3
In what log can I see the success or failure of Storage Accelerator usage?
I have reviewed the below posts but did not really find anything specific.
https://community.commvault.com/storage-and-deduplication-49/storage-accelerator-not-working-912
https://community.commvault.com/commvault-q-a-2/storage-accelerator-who-is-using-it-and-what-are-you-experiences-5395
Thanks.
Ignes